uzgwuefgz
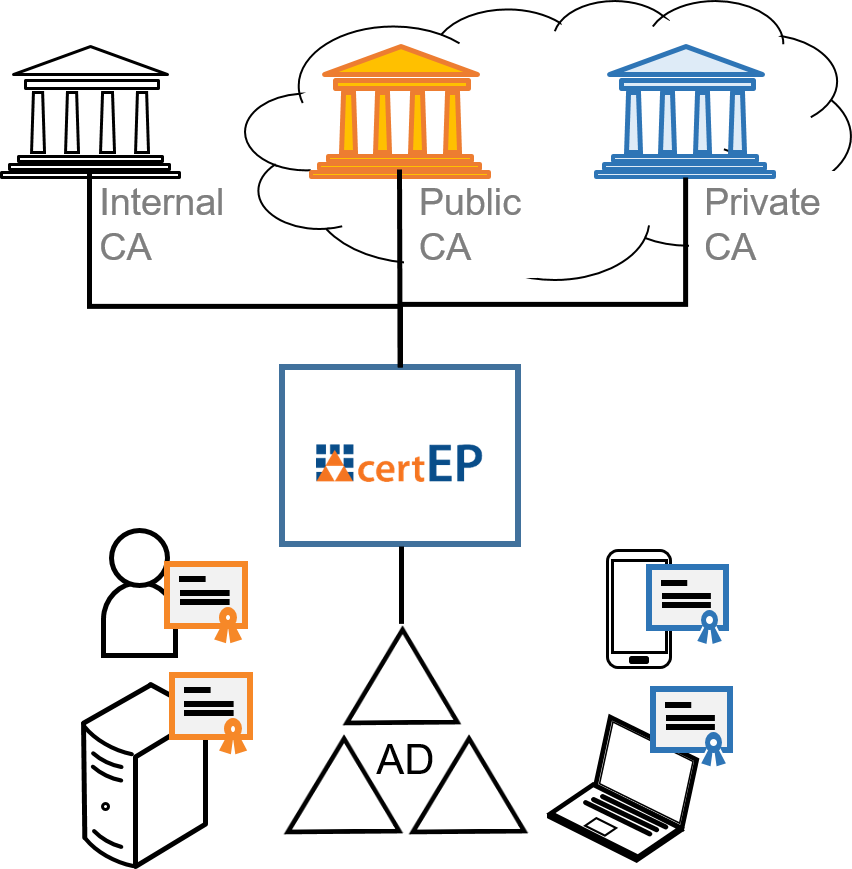
Certificate Enrollment Proxy
Windows auto-enrollment from a CA of your choice. Provide certificates from public or private CAs to your AD users and computers.
Public CA
Provide S/MIME certificates from a trusted public CA for e-mail encryption and digital signature to your users.
Managed PKI
Replace resource consuming Microsoft CAs by managed private CA services in the cloud.
Open Source CA
Upgrade your internal Open Source PKI for native Windows certificate enrollment.
"Secardeo certEP is used by global corporations for the auto-enrollment of hundreds of thousands of user and computer certificates from non-Microsoft CAs."
Extend your AD integrated PKI and keep it flexible!
- Add a public CA to your Active Directory easier than a Microsoft CA.
- Replace your internal Windows PKI by cloud-based private CAs like AWS with just a few clicks.
- Keep the option to change the CA provider flexibly.

Machine auto-enrollment with your preferred CA.
- Perform native Windows auto-enrollment with non-Microsoft CAs.
- Connectors for CA products and Open Source like DogTag, OpenXPKI, EJBCA.
- Connectors for cloud-based private CA services like AWS.
- SCEP-based auto-enrollment via NDES.
- Server-based auto-enrollment for CAs that don't support MS template extension.
- Automatic control for duplicate certificate requests.
- Integration with Intune through standard certificate connectors.
- Connect with multiple CAs with one certEP instance.

How it works
The Secardeo Certificate Enrollment Proxy (certEP) is a component that resides between the Windows clients and the issuing CA. The certEP acts as a Windows enterprise CA towards Windows clients and it supports manual certificate enrollment and certificate autoenrollment from a non-Microsoft CA. This is done by using standard protocols and native tools without the need for distributing proprietary client software. The client is triggered automatically by a group policy and generates a certificate request based on a certificate template in Active Directory. certEP receives the certificate requests, enhances them with the required attributes and forwards them to the issuing CA. certEP uses Microsoft certificate template information to process certificate requests. After receiving the issued certificate from the CA, it is passed to the requesting Windows client. Additionally, the certEP supports key archival, e.g. for S/MIME certficates. Private keys can be archived by encrypting them by KRA certificates. Certificate data and keys are stored reliably in an SQL database. By this, S/MIME certificates and private PKI keys may be automatically recovered and securely distributed to mobile devices using Secardeo certPush.
A series of CA backends is already provided in the product:
- Open Source PKI servers like EJBCA, OpenXPKI or DogTag
- Commercial CA servers like Red Hat, MTG, or even a Microsoft CA
- Public Cloud CA services like SwissSign, DigiCert or GlobalSign
- Private Cloud CA services like AWS or SwissSign



